Streamline Your Log Data Analysis with Log Parser Lizard
Unlock the power of efficient log parsing and data querying with Log Parser Lizard. Our software empowers you to quickly extract critical insights from logs using SQL queries. It features a user-friendly Graphical User Interface (GUI) for Microsoft Log Parser 2.2, a file parsing engine from Microsoft, compatible with all versions of Windows.
Ideal for developers, administrators, auditors, and information security teams, Log Parser Lizard facilitates SQL querying on various structured log data types. These encompass web server logs, Windows system events, and application log files such as log4j, log4net, nlog, and serilog, in addition to CSV, TSV, JSON, and XML formats. The software also supports querying databases on remote servers and is compatible with Microsoft SQL Server, SQLite, MySQL, and OLE DB, among others. With Log Parser Lizard, tasks in log data analysis, threat detection, data collection, exporting, visualization, business intelligence (BI), reporting, and ETL are simplified and more effective.
Efficiently analyze log files with SQL queries using Log Parser Lizard, eliminating the need for database storage:
SELECT DISTINCT src-ip FROM firewall.log WHERE action='DROP'
SELECT TOP 100 * FROM c:\webserver.log WHERE sc-status <> 200
SELECT cs-uri-stem FROM c:\InetPub\Logs\ex*.log
GROUP BY cs-uri-stem HAVING COUNT(*) > 50
SELECT to_lowercase(extract_extension(cs-uri-stem)) AS PageType, SUM(sc-bytes)
FROM ex131118.log, ex131119.log GROUP BY PageType
Enhance your log data navigation and comprehension with the intuitive GUI of Log Parser Lizard, making the process straightforward and effective.
Log Parser Lizard: Every File Becomes a Queryable Database
MS Logparser and Log Parser Lizard are indispensable for system administrators and developers, optimizing tasks such as forensics, debugging, log collection, big data analysis, data visualization, and reporting. Their integration into data management processes is crucial for efficiency and insight.
- Trusted by thousands of users worldwide for its reliability and functionality.
- With over a decade of industry presence, our solution is recognized for its established expertise.
- Certified as safe and secure, as evidenced by our clean status on VirusTotal.
- Offers superior features compared to leading premium products, yet remains accessible and budget-friendly.
Transform your log data analysis with Log Parser Lizard. Download now to elevate your data-driven strategies and unlock new levels of productivity in your log and data analysis tasks.
Favorite Features Among Our Users:
SQL Log Querying
Effortlessly query extensive log data using familiar SQL syntax. Supports complex SQL queries, including functions, joins, unions, and more.
User Interface
We've designed a modern, Office-inspired interface with ribbons and tabs to offer an optimal user experience, especially for professionals who spend significant time analyzing log files.
Advanced Query Editor
Our query editor features syntax highlighting, auto-completion, code snippets, query constants, and inline VB.NET code.
Query Management
Efficiently organize your Log Parser Lizard queries with our effective query management feature.
Data Navigation and Visualization
The output table is not just a data grid but offers advanced features like sorting, grouping, searching, filtering, conditional formatting, formula fields, and column choosing. Generate Excel, HTML, MHT, or PDF reports, create charts for enhanced readability, and automate processes via command line.
Advanced Data Filtering
Utilize Excel-like UI elements for advanced filter expression creation, from Query Builder and Instant Find to Auto-Filter row.
Handle Large Log Files
File size is not a limitation. Process any number of extremely large files swiftly, dependent on your hardware.
Support for Custom Log Formats
Use Regular Expressions and Grok to parse unstructured data into a structured, queryable format. Supports compressed and/or encrypted .gz logs and log4net/log4j XML formats.
Pivot Tables and Tree Maps
For multidimensional analysis and data mining, we offer advanced pivot tables and tree maps that provide unparalleled operational insights.
Intuitive Dashboards
Easily build dashboards by dragging and dropping UI elements like Charts, Pivot Tables, Data Cards, Gauges, Maps, or Grids. Handle everything from data-binding to filtering within Log Parser Lizard.
WYSIWYG Report Designer
Our WYSIWYG Report Designer combines the simplicity of a word processor with the capabilities of a banded report designer.
Web API Server
The built-in Web Server enables query execution with JSON output, typically for integration with external data analysis software. Also, access query results remotely via your web browser.
Printing and Data Export
MS Logparser incorporates an ETL data pipeline for data collection, transformation, and SQL Server data store loading. Log Parser Lizard supplements this with a robust printing and data export engine, supporting a wide range of file formats including XLS, XLSX, PDF, RTF, TXT, MHT, CSV, HTML, and various image formats.
Optimized for Performance
Engineered to meet your most demanding requirements, Log Parser Lizard is always fast and responsive, regardless of the data set size or complexity.
Explore Additional Features
To discover even more features, help files, and examples, download Log Parser Lizard now.
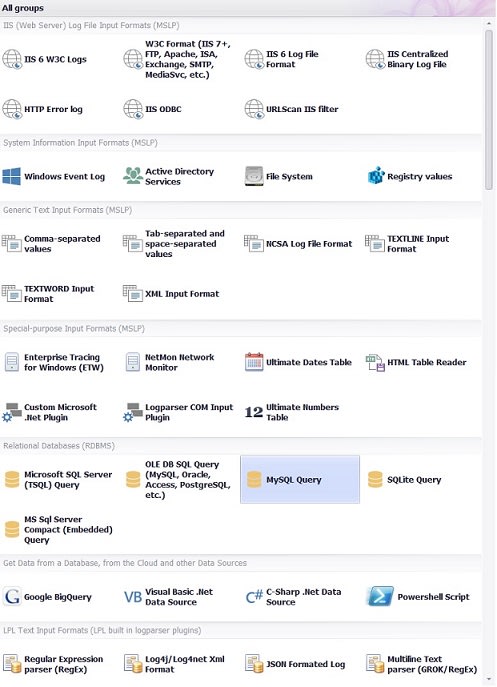
All available input formats:
Log Parser Lizard stands as the premier GUI for Microsoft Logparser, offering unmatched capabilities and flexibility. This powerful query tool delivers universal SQL access to a variety of text-based data, including log files, XML files, and TSV/CSV text files. It also excels in parsing text files with Regular Expressions and GROK. Beyond text data, it adeptly handles essential Windows data sources like Windows Event Log, IIS logs, the registry, the File System, and Active Directory services. For enhanced customization, developers can create Microsoft VB.Net Plugins to extend LPL's functionality. Below is a comprehensive list of all supported input formats:
- W3C Input Format - Parses log files in the W3C Extended Log File Format: Microsoft Internet Information Services (IIS), FTP, Apache, Exchange Tracking, SharePoint, Personal Firewall, Microsoft ISA Server, Windows Media Services, Simple Mail Transfer Protocol (SMTP), etc.
- Windows Event Log - Reads event information from local and remote System, Application, Security, and custom event logs, as well as from Event Log backup files (.evtx).
- Active Directory Services - Enumerates Active Directory objects using SQL.
- Comma-separated values (CSV) - CSV text files are generated by a large number of applications and tools, including Microsoft Excel and PerfMon.
- Tab-separated and space-separated values (TSV) - This format is also the output of many command-line tools.
- Regular Expression Enhanced - Most flexible for parsing text-based log files (supports Regular Expressions and GROK aliases) - any text file is a database.
- Log4j and Log4net XML Format - Apache log4j/log4net XML file format.
- JSON Formatted Log - Reads JSON formatted log files.
- GROK/RegEx Text Parser - Grok is the best way to parse unstructured log data into something structured and queryable. Instead of writing complex regular expressions, use the simple Logstash GROK syntax to quickly build a reader of text-based files - easiest to use, yet powerful.
- XML Input Format - Multiple XML documents and configuration files can be parsed in different ways.
- TEXTLINE Input Format - Parses text files in any format not supported natively. Better than grep.
- IIS W3C Logs - MS IIS web sites logging in the W3C Extended format.
- File System - Better use SQL to enumerate the files and directories.
- Media Files - Use SQL to enumerate video, image, and audio files and get the metadata info.
- Registry values - Enumerates local or remote registry keys and values.
- Logparser COM Input Plugin - With custom plugins, you can query any data source.
- IIS Log File Format.
- IIS Centralized Binary Log File.
- Enterprise Tracing for Windows (ETW).
- Multi-line RegEx (Log4Net or NLOG) Input Format.
- SQL Server T-SQL Query - Use LPL to query relational databases too.
- C# (C-Sharp) .Net Data Source - Run simple C# code and display data in grid.
- HTTP Error log.
- IIS ODBC.
- NCSA Log File Format.
- NetMon Network Monitor.
- TEXTWORD Input Format.
- URLScan IIS filter.
- RegEx Input Format.
- OLE DB SQL Query (MySQL, Oracle, Access, PostgreSQL, etc.).
- Text file RegEx Input Format.
- Google BigQuery.
- Ultimate Dates Table.
- Ultimate Numbers Table.
- HTML Table Reader.
- Excel File Reader.
- Visual Basic .Net Data Source.
- PowerShell Script.
- Microsoft SQL Server Compact Edition (CE).
- SQLite.
Free Premium Features:
Log Parser Lizard is completely free for all users, catering to a diverse array of applications:
- Commercial entities can fully use all features, but without the expectation of support.
- Individuals using it for personal, non-profit, or profit purposes at home have access to all features, with no assurance of support.
- Educational institutions and students involved in learning, training, and research can utilize all features without any support.
- Government agencies at all levels—local, state, federal, or international—can employ all features, but may not receive support or any additional clarifications.
Activation is straightforward, without the need for additional downloads. You can start in under a minute.
Important: Log Parser Lizard is free for all these users, but requests for support may not be provided. If you require any kind of support, this software may not be suitable for your needs.
What they say about Log Parser Lizard:
-
Scott Hanselman: „ What's this? Oh YES. It's intellisense and tooltips, baby! I can't say how much faster this tool made me once I had figured out LogParser. It's funny how you have to suffer at the command line before you can really appreciate a good GUI. “- Analyze your Web Server Data and be empowered with LogParser and Log Parser Lizard GUI
" LogParser is good, we know, but LogParserLizard is great." - Scott Hanselman's Ultimate Developer and Power Users Tool List for Windows - Scott Hanselman is a former professor, former Chief Architect in finance, now speaker, consultant and works for Microsoft as a Principal Program Manager, aiming to spread good information about developing software. They say Scott Hanselman is the Chuck Norris of .NET.
-
Russ McRee : " You’re probably familiar with Log Parser, but I’ll bet you didn’t there was a great GUI-based tool with which to leverage its raw power with ease. Log Parser Lizard is one of those indispensable tools that treads lightly on your system but offers a huge bang for the buck. " - toolsmith: Log Parser Lizard - Russ McRee works for Microsoft's Online Services Security & Compliance team. He writes toolsmith, a monthly column in ISSA Journal. Russ has spoken infosec events such Defcon, Black Hat, RSA,and FIRST and has published in the likes of Information Security, Linux Magazine, (IN)SECURE, and SysAdmin. As an advocate of a holistic approach to information security, Russ' website is holisticinfosec.org. He also serves as a volunteer handler for the SANS Internet Storm Center.
Log Parser Lizard in BOOKS and COURSES:
 Book: Website invasion scene This book is written
in Chinese. Summary: Through the analysis of web log, analysts can use log parser
lizard (LPL) to quickly understand hacking techniques, and then fix vulnerabilities.
This book introduced the Information Security OWASP TOP 10 (information security)
and the basic operation of log parser lizard (LPL) software.
Book: Website invasion scene This book is written
in Chinese. Summary: Through the analysis of web log, analysts can use log parser
lizard (LPL) to quickly understand hacking techniques, and then fix vulnerabilities.
This book introduced the Information Security OWASP TOP 10 (information security)
and the basic operation of log parser lizard (LPL) software.
Course: Log Parser Fundamentals By Robert Boedigheimer
Learn how to use Log Parser to write queries against many different input formats. Robert Boedigheimer works for Schwans Shared Services, LLC providing business solutions with web technologies. Robert has been developing web sites for the past 15 years. He is an ASP.NET MVP, an author, and a 3rd degree black belt in Tae Kwon Do. Robert regularly speaks at national and international events.
Log Parser Lizard is mentioned on RSA Conference
 RSA
Conference is a cryptography and information security-related conference, currently
held annually in San Francisco, California, United States; London, England; and
Chengdu, China. It is a forum for IT professionals to gather and share the latest
knowledge and advancements in the area of Internet security.
RSA
Conference is a cryptography and information security-related conference, currently
held annually in San Francisco, California, United States; London, England; and
Chengdu, China. It is a forum for IT professionals to gather and share the latest
knowledge and advancements in the area of Internet security.
Numerous books on Google and Amazon mention LPL as an indispensable tool for log monitoring and data analysis.
What they say on Twitter:
-
Super nice UI, made some custom queries and it worked like a charm for tracking Hafnium activity! pic.twitter.com/Fq5i3ECgKY
— Darkoperator (@Carlos_Perez) March 15, 2021 -
Log Parser Lizard + Log Parser 2.2 + IIS logs = 😍🥰😍 pic.twitter.com/PUzMNcckQO
— Chad (@CG_iSecurity) February 9, 2021
Log Parser Lizard has consistently been awarded top ratings by independent testing labs and recommended by reviewers worldwide.
DOWNLOAD THE INSTALLER
If the download doesn't start automatically, please use this direct download link for immediate access. Rest assured, the installer (Windows MSI package) is verified as completely clean on VirusTtoal.com and is available at no cost.